This is the text of a post I was invited to contribute to the Institutional Web Managers Workshop (IWMW) Blog as a retrospective to a presentation that Joe gave at the Workshop in 2009.
When Joe Nicholls and I started our conversation back in 2007 on what the IT Services role should look like in the age of “disruptive technologies”, we had a vision that things were never going to be the same again. Indeed in a farewell valedictory at the Welsh Universities IT Services Gregynog Colloquium in 2010 I gave a talk entitled “So that’s it for IT Services … or is it?” after previously writing “We’re all doomed …“. Therefore when Brian invited me to reflect on the relevance of the talk “Servicing ‘Core’ and ‘Chore’” that we presented at IWMW 2009 to the institution today, it set up a whole stream of thoughts running – which have taken some time to commit to words.
First of all I’m extremely grateful for two recent posts by Derek Law (on this blog) and Martin Weller (on the Ed Techie blog) which gave me the courage to proceed when I was beginning to feel that I had no place, being now a number of years out of active institutional web and IT Services involvement, to express any views – let alone suggest they might be relevant! Apparently I’m not completely out of step.
Essentially “‘Core’ and ‘Chore'” is about giving a different perspective – in fact a users perspective – on what an IT Service function needs to deliver in terms of service offering. It is an explicitly user-centric view of IT Services, as it looks to provide the user with the tools THEY require, and with the support THEY need to make full use of them. This is what we have called enablement. As a precursor to enablement, you need to go through a process of envisioning the possibilities that are available and how they might be incorporated into a users’ way of working and then engagement with the user, and as a result of following this process in partnership with the user, you aspire to deliver excellent education. We presented these ideas in a paper at Eunis 2009.
Just words I hear you say, but look at a few of the slides from Joe’s slideset and then judge the relevance to your institution today.
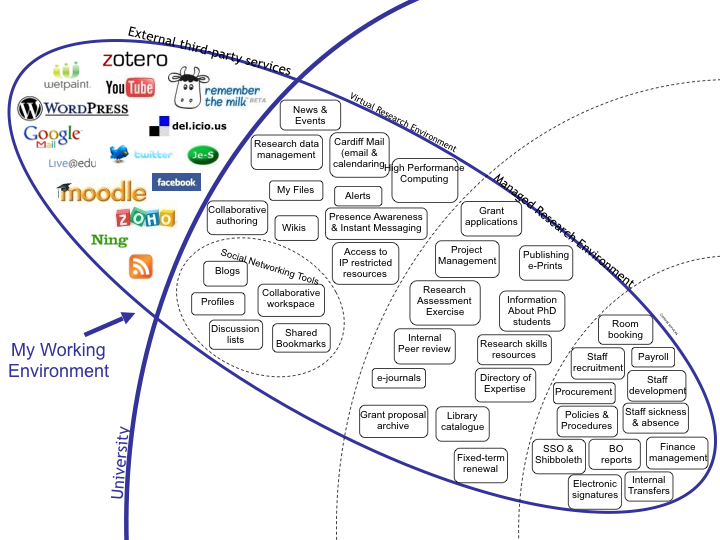
The individual researcher or student has a completely different view of what they want, and need, from an IT service offering. All they require are tools and training in their use to get the educational task done. This is core to them.
For them the interaction with corporate systems is a chore, often an unpleasant diversion from getting things done!
This leads into a conflict because much of what the individual requires is outside the institutional firewall, and by its placement “in the cloud” is “not controllable” by the organisation. I have discussed governance and security elsewhere and previously, and don’t intend to follow that up here. Suffice to say, both issues can be resolved, through trust and education. Working in partnership. Thus we arrive at this seeming impasse …
The ‘core’ services and activities to the institution are the ‘chore’ to the individual. The ‘core’ services and activities to the individual are often not identified by the institution as necessary, or at worst are actively prevented from happening.
I would love to be able to say that I am confident that what Joe and I presented back in 2009 at IWMW has now been committed to the Room 101 of institutional web history as having been acknowledged, accepted and actioned. I fear it hasn’t. In fact I know it hasn’t as the horror stories of failed collaboration across institutions, of difficulties in migrating content into, out of and between institutions, and the failure of the very seemingly straightforward task of ensuring proper archiving of digital content is accessible outside the institution, continue seemingly in an unremitting manner.
So I conclude with just one plea for institutional web managers. I realise that you will most certainly not be in a position to alter institutional strategy, but please just please remember the individual in your service offering. Be prepared to readily provide advice on setting up a personal web presence outside the institution – that means providing advice on getting personal or project domains. Be open to the probability that researchers will want to port content out of institutional systems when they move, or retire, and have a way that enables them to do that easily. Be aware that digital content only lasts as long as it is archived properly – boring I know but time spent now will prevent tears later on. Be an envisioned and engaged web manager, enabling the user to achieve their educational objectives. Your attendance at IWMW 20, suggests that you are well on the way to doing this.